2019.06.19 00:40:14 (1141113419443179520) from Daniel J. Bernstein, replying to "Chris Peikert (@ChrisPeikert)" (1141108481451278337):
Claim made in the paper, under very optimistic assumptions, some of which are stated explicitly: "CSIDH-512 does not achieve the claimed 64 bits of quantum security." Next sentence of the paper: "A more prudent estimate would be closer to 40 + 16 = 56 bits of quantum security."
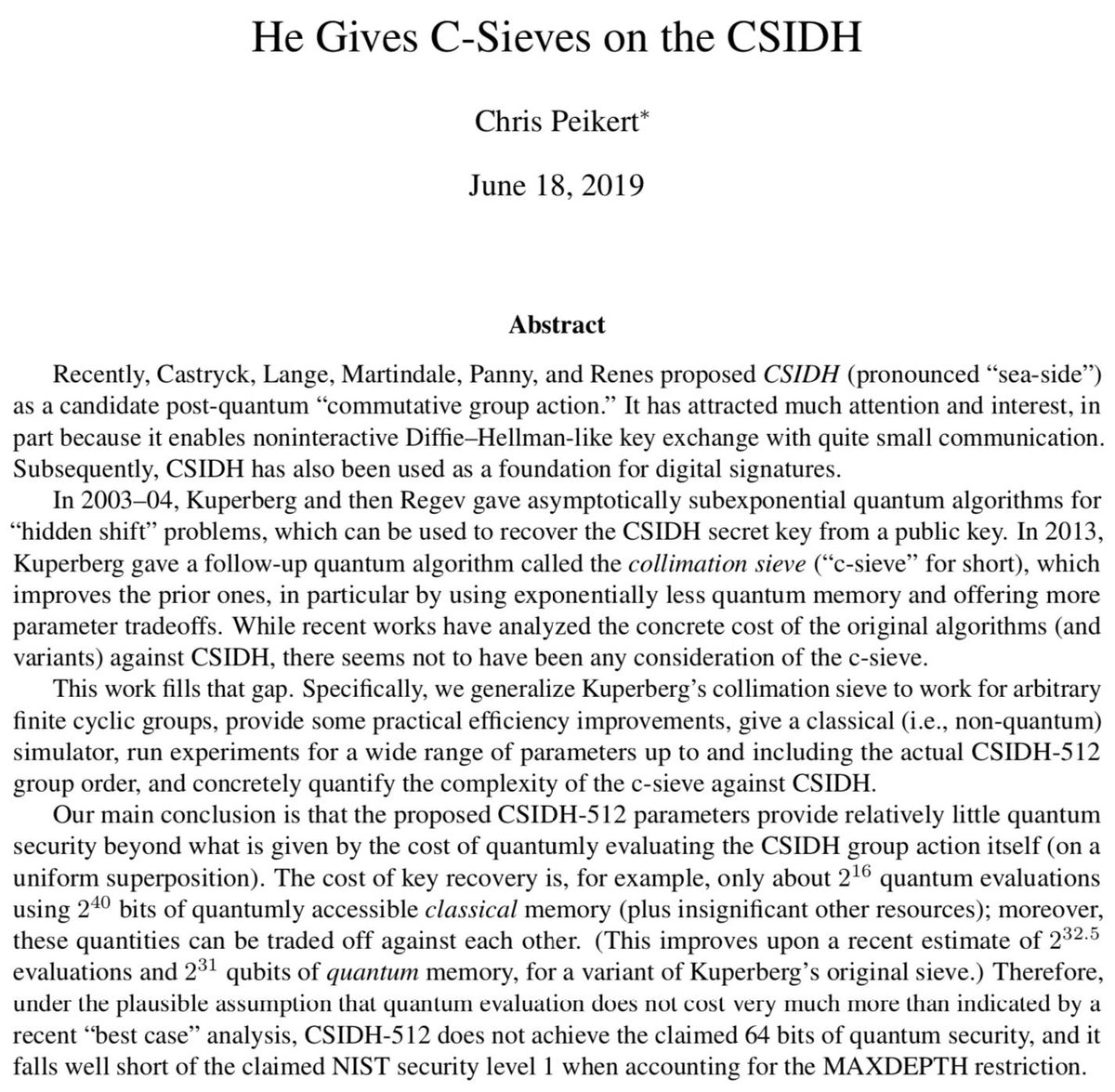
2019.06.18 22:41:37 (1141083566731698176) from "Chris Peikert (@ChrisPeikert)":
🚨 NEW PAPER cryptanalyzing CSIDH using Kuperberg's quantum "collimation sieve." Bottom line: CSIDH-512 key recovery with only, e.g., ~2^16 quantum group-action evaluations and ~2^40 q-accessible classical memory. Paper: http://web.eecs.umich.edu/~cpeikert/pubs/csidh-sieve.pdf Code: https://github.com/cpeikert/CollimationSieve
2019.06.18 23:34:23 (1141096846045171712) from "hanno💉💉💉💉 (@hanno)":
Am I translating this right as "CSIDH is dead"? and does this have implications for other isogeny-based systems? https://twitter.com/ChrisPeikert/status/1141083566731698176
2019.06.18 23:55:54 (1141102259712999429) from Daniel J. Bernstein, replying to "hanno💉💉💉💉 (@hanno)" (1141096846045171712):
No, CSIDH is fine. All known attacks are exponential in n^(1/2+o(1)), and the question is simply how big the o(1) is. For CSIDH-512 in particular, the new paper is claiming a total of 2^56 qubit operations, but this is under very optimistic assumptions for the attacker.
2019.06.19 00:20:37 (1141108481451278337) from "Chris Peikert (@ChrisPeikert)":
The paper does not claim a total of 2^56 qubit operations.